Hello,
In September 2023, Google published CVE-2023-4863 and CVE-2023-5217 to address vulnerabilities in WebP (a compression format for images on the web) and libvpx (a software video codec library) that may result in remote code execution. The subsequent impact to Microsoft products has been documented in the Security Update Guide and the MSRC blog. Google is aware that exploits exist for both vulnerabilities.
These CVEs are both categorised as High Severity and we are notified that “A verified remote code execution exploit is publicly available for one or more weaknesses related to this recommendation.”
Currently we have 4 machines that appear to have Razer Software installations that have this 3rd party component included and are therefore being flagged as affected by both CVE-2023-4863 and a separate (earlier) WebP vulnerability CVE-2023-1999 (I believe the existence of these 2 vulnerabilities are why all 4 of our affected devices are being flagged as High Risk in our vulnerability monitoring system)
N.B. Our vulnerability monitoring system flags the following 2 files as vulnerable on all 4 devices:
| File | File Version | Affected by CVEs |
|---|---|---|
| C:\Windows\Installer\Razer\installer\app\libwebp_x64.dll | 1.1.0.0 | CVE-2023-1999 & CVE-2023-4863 |
| C:\Windows\Installer\Razer\installer\app\libwebp_x86.dll | 1.1.0.0 | CVE-2023-1999 & CVE-2023-4863 |
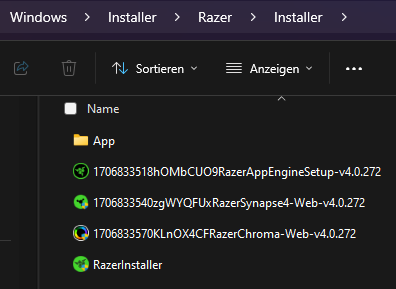
I believe the existence of these 2 files is caused by the installation of Razer Synapse on these devices, At this stage it is unclear exactly which version(s) are installed on each device – So I will need to check via our software discovery to get a better idea of what app (and version) are installed on each device, failing that I will need to check locally on at least one of our machines to carry out an investigation.
The only reference I can find on the Razer site(s) to the C:\Windows\Installer\Razer\* path is this forum article: https://insider.razer.com/razer-synapse-29/delete-c-windows-installer-razer-over-13gb-45177, however as both the affected LibWebP DLL’s exist below the “C:\Windows\Installer\Razer\installer\app” folder; deleting the affected files does not appear to be an option.
The latest Razer downloads can be found via: https://www.razer.com/gb-en/pc/software, specifically for the Current release of Synapse 3: https://www.razer.com/gb-en/synapse-3
Direct download: https://rzr.to/synapse-3-pc-download for “RazerSynapseInstaller_V1.16.0.543.exe”
Another observation: The installer version numbering has no obvious relationship to the actual product version installed (Installer v1.x.x / Product v3.x.x), so it is unclear if this is a newer version than what the user(s) already have installed.
From my searching I can find no Release Notes of any substance anywhere on the Razer sites (Main site (razer.com) or forum (insider.razer.com), so it is anyone’s guess if updates to this product have had the fixes included by now?
Searching (without quotes) on Google for: “CVE-2023-1999 site:razer.com” returns zero results – Indicating there is no mention of this CVE anywhere on the indexed pages of the Razer site(s).
Searching (without quotes) on Google for: “CVE-2023-4863 site:razer.com” returns zero results – Indicating there is no mention of this CVE anywhere on the indexed pages of the Razer site(s).
If it comes to it, a clean re-installation of Razer Synapse could potentially be performed on each device following these instructions: https://mysupport.razer.com/app/answers/detail/a_id/1708
However, Step 8 makes absolutely no mention of the C:\Windows\Installer\Razer\* path, so I’d suspect this would still not resolve the issue.
Can you:
- Confirm if these CVEs have already been fixed in a later version of the Razer software (I assume Synapse 3)?
- Confirm which version of Synapse 3 we need to have installed to remove thse CVEs?
- Confirm which version of the Installer I should use to install the fixed version of Synapse 3?
- Confirm where your product Release Notes are published that state where and when this CVE was resolved in your software?
- Update your Clean re-installation instructions to detail any other the Razer folders that may need to be removed (e.g. below C:\Windows\Installer\Razer)?
- Can you make some major improvements to the manner in which you publish your release notes?so we, as customers of your products(s) know exactly what has been fixed, for what reason and when?
N.B. This is worth a read: https://www.productplan.com/learn/release-notes-best-practices/
I look forward to your answers as soon as you possibly can, so I can resolve these high severity CVEs from my estate.
Thanks in Advance,
Adrian Scott
EUC engineer